To prepare your organization for the cumulative impact of these trends, you will need to consider new and better solutions for next-generation firewalls, application control and visualization, bandwidth management, secure remote access, clean VPN and wireless, and data leakage prevention.
Trend 1: Cloud Consumption
Taking applications to the cloud remains one of the big trends in 2011. Organizations will spend 30 percent more on public IT cloud services, with 33 percent of midsize U.S. firms embracing cloud resources, according to IDC. However, at the same time, non-business-related websites now consume up to 15 percent of available corporate bandwidth, and that figure is rising sharply. As your organization relies more on the cloud to drive lower capital expenditures and improve efficiencies, you will need to deal with two potentially unforeseen impacts.
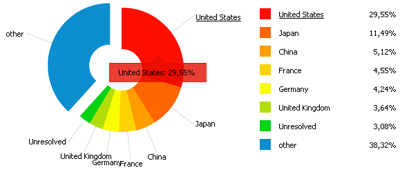
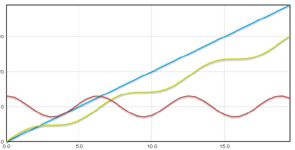
First, the on-premises bandwidth used to access the cloud from the WAN is limited. Therefore, you need to prioritize bandwidth for -- and user access to -- critical applications over lesser-prioritized traffic that is not paramount to the business. To accomplish this, your bandwidth management policy must be able to make increasingly sophisticated distinctions between mission critical cloud-based applications (e.g., Salesforce.com (NYSE: CRM), Oracle (Nasdaq: ORCL), etc.), streaming and latency-sensitive applications (e.g., teleconferencing and VoIP), and business- and personal-use social media and peer-to-peer applications (e.g., Facebook, BitTorrent, etc.).
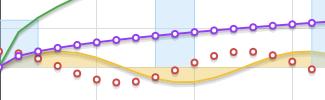
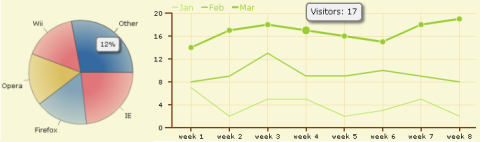
Next-generation firewalls with application intelligence, control and visualization capabilities can help you identify and control exactly what applications are in use and who uses them -- regardless of port or protocol. Moreover, to control network use properly, you can deploy advanced visualization solutions to view application traffic in real-time and adjust network policy based on critical observations.
Second, by putting critical applications in the cloud, your organization encourages employees to spend more time on the Internet. Unfortunately, they will likely access non-business sites as well as business-related sites, exposing your organization to lost productivity and more malware, botnets, and other forms of malicious attacks.
As your organization relies more on cloud-based applications for productivity and business success, you must be increasingly vigilant against Web-borne attacks. As sensitive data now migrates between corporate data centers and cloud data centers beyond your network perimeter, you can no longer think only in terms of network security, but instead must shift focus to information security: achieving security for all your corporate data and applications, regardless of where they are located.
Over the next year, firewall solutions will increasingly augment and enhance traditional on-box malware signature defenses with advanced cloud-based logic to provide comprehensive protection. Security technologies will continue to evolve, presenting tighter and more manageable security solutions for the borderless network. The scope, scale and performance demands of securing a borderless environment will spur the development of massively scalable security architecture solutions.
Trend 2: Virtualization
Virtualization has grown beyond its early hype and has seen much broader deployment. Businesses have consolidated multiple servers and appliances onto fewer physical machines, enhancing both cost-savings and inter-application performance. By next year, organizations will have virtualized nearly half of all server workloads. At least 14 percent of the infrastructure and operations architecture of Fortune 1000 companies will be managed and delivered internally in a virtualized environment.
Consolidating servers and appliances from physical to virtual environments often runs the risk of undermining implicit security and access barriers that previously existed between isolated applications. You can help preserve this legacy security by deploying next-generation firewalls using deep packet inspection and application control between virtualized server environments.
As your organization pursues on-premise virtualization of mission-critical applications, you will need to scan and secure higher volumes of inbound and outbound traffic at high-speed rates of 10 GB and more. To this end, businesses will require higher performance firewall technologies that feature real-time reassembly-free deep packet inspection, multicore processing platforms, and performance-optimized architecture.
Moreover, as with cloud-based resources, some application traffic will inherently have a greater business value. You can prioritize and control application and user traffic using application-intelligent Next-Generation Firewalls that allow implementation of a granular policy over bandwidth allocation based on application type.
Trend 3: Mobility
Smartphones and tablets such as Apple's (Nasdaq: AAPL) iPhone 4 and iPad, or the many devices running Google's (Nasdaq: GOOG) Android OS, have been widely adopted by employees as standard business tools. Much in the way that laptops eclipsed desktops in the workplace a decade ago, mobile devices are now the business tools of choice, and there is no going back. Shipments of mobile devices will outstrip PCs in the next year and a half, according to IDC. However, less than a third of enterprises have a multiplatform policy in place, according to the iPass Mobile Workforce Report. As the market for mobile devices will continue to evolve and shake out, you should take a platform-agnostic approach.
In scenarios where mobile devices are accessing corporate resources from outside the company's perimeter, you need platform-agnostic secure remote access to mission-critical resources. Web-based SSL VPN portals can provide platform-agnostic access from virtually any mobile endpoint, including laptops, PDAs and smartphones.
By filtering SSL VPN traffic through a high-performance next-generation firewall, you can establish a clean VPN to secure both VPN access and traffic. The multilayered protection of a clean VPN enables you to decrypt and decontaminate all authorized SSL VPN traffic before it enters your network environment. In addition, you effectively control data leakage by integrating deep packet inspection, email security, and application intelligence and control to identify sensitive data and prevent it from leaving your network.
Alternately, for scenarios where mobile devices are accessing the Internet from within your perimeter, users can deploy solutions that integrate a wireless switch directly into their next-generation firewall to subject all wireless traffic to clean VPN scanning and application intelligence, control and visualization, thereby maintaining both security and application usage efficiency.
 The Wilsonville Power Systems Development Facility (PSDF) is a research and development center that tests various processes, mainly coal-based technologies, before they are implemented at power supply facilities. In 2006, the growing plant employed 200 people and produced a wastewater flow of about 25 gpm. With its size expected to double in the near future, the facility was required by state and local regulators to start disinfecting its wastewater. Since the existing wastewater treatment facility in Wilsonville was too far away for the facility to connect, the PSDF decided to build its own wastewater treatment facility.
The Wilsonville Power Systems Development Facility (PSDF) is a research and development center that tests various processes, mainly coal-based technologies, before they are implemented at power supply facilities. In 2006, the growing plant employed 200 people and produced a wastewater flow of about 25 gpm. With its size expected to double in the near future, the facility was required by state and local regulators to start disinfecting its wastewater. Since the existing wastewater treatment facility in Wilsonville was too far away for the facility to connect, the PSDF decided to build its own wastewater treatment facility.